Best Online Cybersecurity Degree Programs of 2025
A cybersecurity degree can prepare you to pursue a high-paying, in-demand career. Explore some of the best online cybersecurity programs.At BestColleges.com, we believe in providing accurate and actionable information for students. Our writers, editors, and reporters are constantly asking themselves the question, "What information is vital to students right now?" Answering this question is what drives us. Our mission is to inform students through straightforward, factual content informed by the latest data and trends.
The freelance Integrity Network at BestColleges is comprised of seasoned professionals who bring their expertise to almost every subject relevant to college students, including admissions, college majors, financial aid, and student mental health. Network members review and author content, pulling from their first-hand industry experience and ensuring content is as accurate and up-to-date as possible.
If you're interested in joining our Integrity Network, contact us at media@bestcolleges.com. Integrity Network members typically have a graduate or terminal degree and several years of relevant professional experience.
Explore our full list of Integrity Network members.
3,700+ Nonprofit, accredited colleges analyzed

6,000+ Users connected with programs every month

300+ College and university partners

40+ Expert reviewers
Learn more about our Editorial Policy and Standards and Advertising Disclosure.
 2025
2025Cybersecurity is one of the fastest-growing fields in the country. The Bureau of Labor Statistics (BLS) projects that some careers within the field are projected to experience an over 30% growth in employment over the next decade.
This demand has led to a shift in higher education. A growing number of colleges are launching cybersecurity degrees for the first time. Also, some universities are rolling out colleges dedicated to cybersecurity and related tech disciplines.
Even some of the world’s biggest tech companies, including Microsoft, have invested millions into cybersecurity education initiatives.
If you’re interested in breaking into the field, read on for our list of the best online cybersecurity degree programs, ranked based on affordability, student outcomes, and other factors to help you find the right fit.
Cybersecurity Degree Highlights
- Some cybersecurity jobs are projected to grow around 30% over the next decade.
- An online cybersecurity degree takes around four years (120 credits) to complete.
Source: BLS, BestColleges
Best Online Cybersecurity Schools
How We Rank Schools
To create this ranking, BestColleges sourced the most recent data available from the National Center for Education Statistics and the U.S. Department of Education College Scorecard. We then ranked each school according to the top variables college students selected in our College Choice and Admissions Survey. To learn more, check out our full rankings methodology or read the summary below.
To qualify for our rankings lists, each school must be an accredited public or private, nonprofit institution. Each eligible school was then ranked based on a formula measuring:
 2025
2025- Affordability (30%)
- Student outcomes (30%)
- Reputation (20%)
- Diversity and social mobility (20%)
In addition, we only included colleges with graduation rates in the top third of all online colleges.
Boise State University
Boise, ID4 yearCampus + Online
$5,941
$24,135
84%
56%
Why We Chose This School
BSU's online bachelor's in cyber operations and resilience program combines a customizable curriculum with excellent flexibility. BSU offers stackable credentials, certification pathways, and practical learning opportunities. These elements are built into a 100% online asynchronous program that supports full-time or part-time enrollment.
Courses emphasize real-world applications of academic content, adding a valuable hands-on dimension. The accelerated curriculum accommodates everyone from high school and community college students to working adults seeking to pursue further education.
Highlights
- National Security Agency-designated Center of Academic Excellence
- Strong industry partnerships
- No math or technical knowledge required
Know Before You Apply
- Extensive academic foundation requirements
- In-person internship recommended
$7,236
$24,573
78%
26,727
Public
Yes
$5,941
$24,135
Boise, ID4 yearCampus + Online
$5,941
$24,135
84%
56%
$7,236
$24,573
78%
26,727
Public
Yes
Why We Chose This School
BSU's online bachelor's in cyber operations and resilience program combines a customizable curriculum with excellent flexibility. BSU offers stackable credentials, certification pathways, and practical learning opportunities. These elements are built into a 100% online asynchronous program that supports full-time or part-time enrollment.
Courses emphasize real-world applications of academic content, adding a valuable hands-on dimension. The accelerated curriculum accommodates everyone from high school and community college students to working adults seeking to pursue further education.
Highlights
- National Security Agency-designated Center of Academic Excellence
- Strong industry partnerships
- No math or technical knowledge required
Know Before You Apply
- Extensive academic foundation requirements
- In-person internship recommended
Hilbert College
Hamburg, NY4 yearCampus + Online
$27,400
$27,400
95%
40%
Why We Chose This School
Hilbert College Global's BS in cybersecurity program explores both the technical and managerial sides of cybersecurity, delivering content in small classes. The program has a strong secondary emphasis on professional ethics, which complements its focus on investigative techniques and digital forensics.
Asynchronous course delivery and eight-week semesters can help learners move through the program quickly. Students can transfer in up to 90 credits, potentially reducing the time to graduation to just one year.
Highlights
- 12-to-1 student-to-faculty ratio
- Excellent ROI profile
- Six annual start dates
Know Before You Apply
- Extensive general education requirements
- Internship required
- No specialized accreditation
$17,955
$17,955
66%
877
Private
Yes
$27,400
$27,400
Hamburg, NY4 yearCampus + Online
$27,400
$27,400
95%
40%
$17,955
$17,955
66%
877
Private
Yes
Why We Chose This School
Hilbert College Global's BS in cybersecurity program explores both the technical and managerial sides of cybersecurity, delivering content in small classes. The program has a strong secondary emphasis on professional ethics, which complements its focus on investigative techniques and digital forensics.
Asynchronous course delivery and eight-week semesters can help learners move through the program quickly. Students can transfer in up to 90 credits, potentially reducing the time to graduation to just one year.
Highlights
- 12-to-1 student-to-faculty ratio
- Excellent ROI profile
- Six annual start dates
Know Before You Apply
- Extensive general education requirements
- Internship required
- No specialized accreditation
Kennesaw State University
Kennesaw, GA4 yearCampus + Online
$5,562
$19,630
69%
62%
Why We Chose This School
KSU's online BS program in cybersecurity takes an interdisciplinary approach, combining technical coverage of cyber operations with information assurance, information technology, and criminal justice perspectives. KSU employs expert faculty members from these fields to lead courses.
The four-year, 120-credit program emphasizes security policy, regulatory compliance, and computer system security administration. KSU is officially designated as a National Center of Academic Excellence by the National Security Agency in these areas.
Highlights
- Relatively low tuition
- Excellent recruitment history
- Specialize in systems security, network security, or cybercrime
Know Before You Apply
- Minimum "C" grade required for all major coursework
- Internship recommended
- Selective admissions
- 48% graduation rate
$5,328
$19,188
79%
45,152
Public
Yes
$5,562
$19,630
Kennesaw, GA4 yearCampus + Online
$5,562
$19,630
69%
62%
$5,328
$19,188
79%
45,152
Public
Yes
Why We Chose This School
KSU's online BS program in cybersecurity takes an interdisciplinary approach, combining technical coverage of cyber operations with information assurance, information technology, and criminal justice perspectives. KSU employs expert faculty members from these fields to lead courses.
The four-year, 120-credit program emphasizes security policy, regulatory compliance, and computer system security administration. KSU is officially designated as a National Center of Academic Excellence by the National Security Agency in these areas.
Highlights
- Relatively low tuition
- Excellent recruitment history
- Specialize in systems security, network security, or cybercrime
Know Before You Apply
- Minimum "C" grade required for all major coursework
- Internship recommended
- Selective admissions
- 48% graduation rate
Why You Should Get an Online Cybersecurity Degree
Learn up-to-date field practices: A cybersecurity degree will prepare you with the best practices for work in the field, such as implementing secure network protocols, responding to cyber incidents, and protecting sensitive data from threats.
Work across multiple industries: Cybersecurity professionals are in demand across different industries as organizations and companies need to protect sensitive data, prevent cyberattacks, and comply with security regulations.
Stand out in a growing field: A bachelor’s in cybersecurity can help you stand out from the competition when applying for jobs.
Work with new technologies: Many programs are incorporating AI into their curriculum, helping students gain exposure to emerging technologies and stay relevant in a rapidly evolving field.
Benefits of Getting a Cybersecurity Degree Online
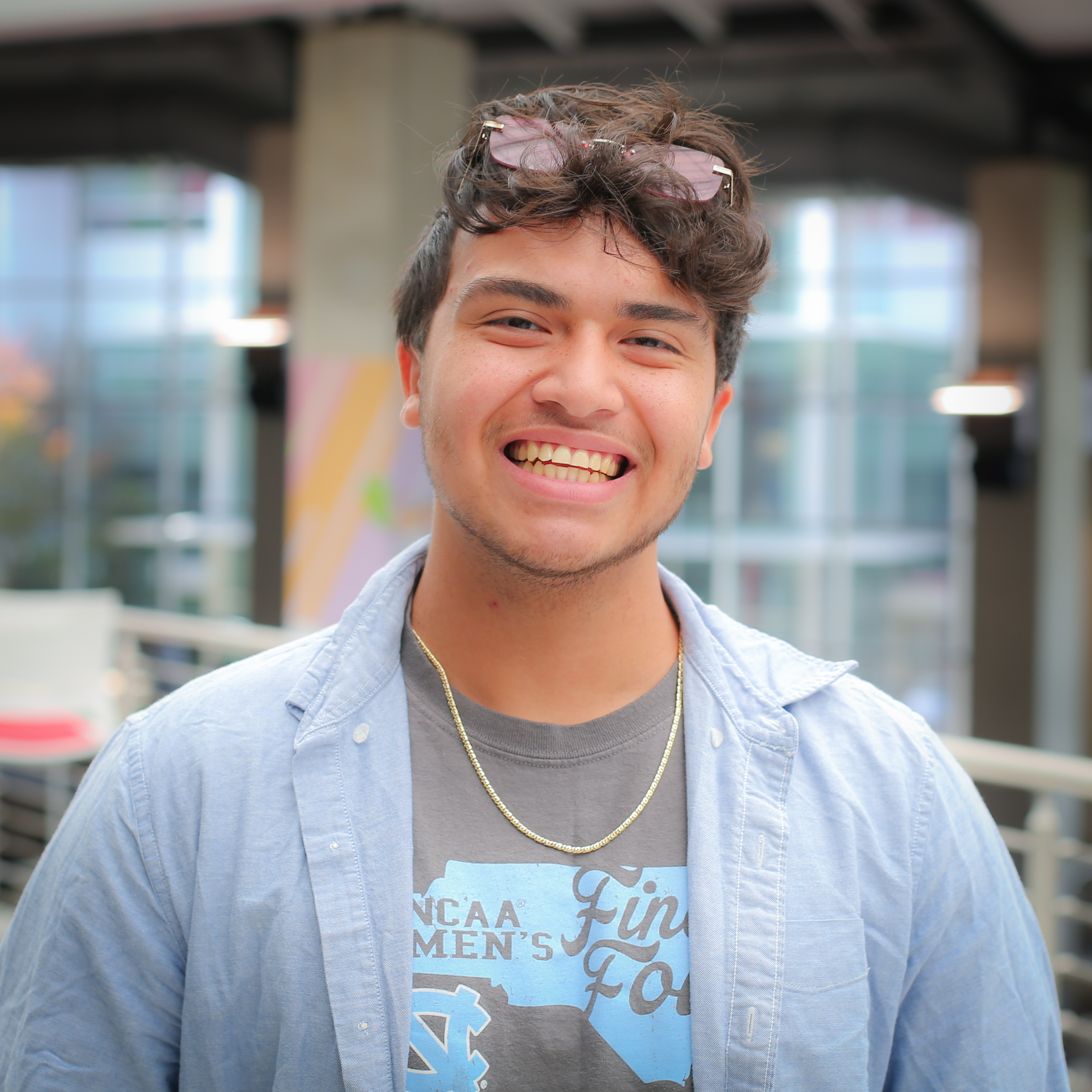
Our 2024 Online Education Trends Report found that 94% of online STEM program students and graduates told us they would recommend online education to others.
More than half of those students said their curriculum helped them explore different career options.
The same survey found that more than three-quarters of online STEM students and graduates said an online learning environment was equal to or better than learning on campus.
How to Choose the Best Cybersecurity Program for You
Here are the key factors you should consider when choosing the best cybersecurity program for you:
How Much Does an Online Cybersecurity Degree Cost? (2019-2020)
Avg. Tuition & Fees
$11,480
Avg. Net Price
$7,384
Source: NCES PowerStats
According to the National Center for Education Statistics (NCES), an online bachelor’s degree in cybersecurity usually costs less than $12,000 — and that price is further cut down to under $7,500 with financial aid.
Once you enroll in a bachelor’s degree program, contact the school’s financial aid department to ask about available grants and scholarships. Also, make sure to fill out the Free Application for Federal Student Aid (FAFSA) to check if you qualify for federal grants.
There are also some cybersecurity-specific scholarships available. For example, the Department of Defense offers a free college program to cybersecurity students if they commit to working for the department after graduation.
Find Financial Aid for Your Cybersecurity Degree
How Long Does It Take to Get a Cybersecurity Bachelor’s?
Typical # of Credits
120 Credits
Typical Program Length
4 Years
Online bachelor’s degrees usually take 120 credits and around four years to complete. However, there are some cybersecurity programs that offer accelerated formats to help you finish your degree faster.
Transferring credits from a previous college can also help you cut down on the years it takes to complete the degree — as well as the cost. Each college has its own requirements for transferring credits, so make sure to research whether your previous classes might qualify.
Ultimately, the speed at which you finish your degree will depend on your schedule and whether you decide to enroll full time or part time. Online programs tend to offer highly flexible schedules, so you might be able to take on more than the typical 12-15 credits per semester to finish your degree faster. However, if you take classes part-time while working, it will likely take longer to complete your degree compared to a full-time student.
What Can You Do With a Cybersecurity Degree?
The BLS projects a growth of over 30% for information security analyst jobs over the next decade. But that isn’t your only career option with a degree in cybersecurity.
With a cybersecurity degree, you could also step into other high-earning roles in the field, such as information systems managers and database administrators. These roles had a median annual salary of more than $100,000 in 2024.
| Job | Median Annual Salary (May 2024) | Description |
|---|---|---|
| Information Security Analyst | $124,910 | Implements cybersecurity measures on an organization’s IT infrastructure |
| Computer and Information Systems Manager | $171,200 | Keeps an organization’s computer systems up to date and running smoothly |
| Database Administrator | $122,100 | Works to ensure an organization’s databases are safe and legible |
| Network and Computer Systems Administrator | $96,800 | Manages communications infrastructure for an organization |
Learn More About Cybersecurity Jobs
Cybersecurity Degree Concentrations
Cybersecurity is a broad field, and concentrations tend to vary by school. Some programs offer certifications in data management and analysis, while others might offer specializations in software development or cloud computing.
Cybersecurity is also often also offered as a concentration within information technology and data analytics degrees.
Is a Cybersecurity Degree Worth It?
A bachelor’s degree in cybersecurity usually costs less than $12,000, and the degree can lead to several high-paying careers that earn more than $100,000 per year. These factors make this degree a worthwhile option with a solid return on investment.
Education Beyond a Bachelor’s in Cybersecurity Degree
A bachelor’s degree in cybersecurity can get you started in the industry, but a master’s degree can help you further specialize your skills and stand out during your job hunt. For example, a master’s degree in cybersecurity can help you move into leadership positions within the field.
Also, keep in mind that some bachelor’s degree programs offer an accelerated pathway to earn a master’s degree by taking credits that count toward both an undergraduate and a graduate program. Some master of business administration (MBA) programs also offer concentrations in cybersecurity.
Frequently Asked Questions About Cybersecurity Degrees
The median annual salary for an information security analyst is $124,910, according to the Bureau of Labor Statistics, but some cybersecurity professionals earn well beyond that figure. For example, the top 10% of information security analyst professionals earn more than $186,420.
Explore More College Resources

Best Cybersecurity Bootcamps Guide
The best cybersecurity bootcamps offer flexible formats and convenient class times. Learn more about cybersecurity bootcamp costs and salaries in the field.

by Holland Webb
Updated September 18, 2024

Best Online Cybercrime Programs
Earning a cyber crime degree online can lead to a lucrative and in-demand career. Explore costs, career opportunities, and typical courses.

by Marisa Upson
Updated February 13, 2024
Other Technology Resources
Technology
programs
careers